
- What is shadow IT?
- What are the risks of shadow IT?
- What causes shadow IT?
- Examples of shadow IT
- How to reduce shadow IT and control spend in 5 steps
- How Ramp helps you regain control over shadow IT spending
- Bringing shadow IT into the light
Direct purchasing of SaaS applications and other non-approved software by employees is making it impossible to protect some organizational data, according to almost half of all executives surveyed in a recent poll.
The IBM/Forbes report also revealed that 60 percent of organizations exclude this problem—known as shadow IT—from their cybersecurity assessments. Unfortunately, the implications of this problem can be quite disastrous, including everything from data loss risks to unaccounted for spending.
What is shadow IT?
Shadow IT is the use of unauthorized or non-standard information technology solutions in organizations. Because software is so easy for anyone to acquire, employees can easily buy and use hardware and SaaS applications without notifying IT or obtaining budget approval.
What are the risks of shadow IT?
1. No oversight into spend
This is a big headache for finance teams and IT managers alike. Without accurate knowledge of IT spending, your finance team can’t brief the executive team with a full picture so they can make important decisions about IT resourcing. And as every modern business leader knows, IT touches every part of the business. When it’s not in good shape, this can create cascading problems across other departments.
2. IT redundancies and security risks
Shadow IT users may source new applications that overlap with existing solutions in your environment that IT has approved. Not only does this create redundancies across your cloud-first environment, but IBM reports that 46% of IT leaders believe that the purchase of unsanctioned software “makes it impossible to protect all their organization’s data”.
3. Data silos
Data needs to be a team sport. If your key people don’t have access to the same data about your operations, performance, and service levels then how can you make the right decisions together as a team? Data silos are one of the most pernicious outcomes of shadow IT, because they grow over time and can become harder and harder to cut back once they do.
4. Stranded financial data
Disorganized and disparate data is not just an in-house problem. As reported in CIO Magazine, shadow IT creates confusion across financial reporting systems, which puts your organization at risk for additional audit fees and SOX violations.
What causes shadow IT?
Employees tend to engage in shadow IT so that they can bypass the often slow and bureaucratic security policies created and enacted by the company's IT department. But there are myriad causes of shadow IT, which can include:
1. Internal frustration with IT services
Many employees turn to shadow IT out of frustration. This can happen when:
- An IT department is too slow to respond to service requests
- An IT department is hindered by legacy software that doesn't have the needed functionality
- An IT department isn’t providing modern solutions to the problems
2. The business or finance team has not set a clear IT expense policy
Many companies will have a budget set aside for software that fits the needs of each department. Unfortunately, some businesses lack an open policy that regulates how employees purchase and use devices and third-party apps. Others may have policies that are too strict, where they restrict access to useful solutions. This can bury the IT and accounting department in requests, approvals, and busywork. Along with these points, if there is oversight in creating an expense policy for IT, the following can happen:
- Budgets get misused since there aren’t clear policies established.
- Businesses can face a surge in unapproved software
- IT becomes consumerized in a way that makes shadow IT more attractive to employees.
3. Sign-offs and reimbursement are chaotic
Chaotic expense policies and reimbursement policies can be just as problematic as non-existent ones. If it’s too hard for a self-starting employee to get approval for a useful solution, then they’re going to take matters into their own hands. This can create a big issue for finance teams, where shadow IT casts an ever-growing darkness over expenditure that just can’t be seen until it reaches a crisis point.
4. Finance lacks control over IT spending
When employees are unsure if there are funds to pay for a new computer or other necessary expenses, employees will look for other options— and this can lead to maverick spend. Without a solid expense policy, or dedicated spend management solutions, staff have no idea if security devices or software applications are approved.
Examples of shadow IT
A common example of shadow IT is when employees buy devices or software for work that are not approved by the company expenses policy. Other examples of shadow IT include the unapproved purchases of:
- Physical devices such as flash drives
- Personal messaging apps on work devices
- Productivity apps like Asana and other cloud-based services
Shadow IT increases the risk of sensitive commercial data getting into the wrong hands, either through information-gathering activities in the background of apps, or through the obtaining of information by unauthorized employees within a network. Shadow IT represents a problem for all departments and should be tackled through proactive policy and practice-setting led by both the finance and IT departments.
How to reduce shadow IT and control spend in 5 steps
The good news is you can get shadow IT under control. And with more of your employees working from home and looking to find new ways to drive projects forward and maintain their productivity, it's more important than ever to address shadow IT early.
Step 1: Educate your employees about shadow IT
Shadow IT is a problem that can only be solved by employee education and awareness. Tell your teams about the risks associated with shadow IT by training them on security best practices. You can also:
- Ask employees to disclose the external solutions they are using to handle company data
- Task IT with establishing security protocols for the use of these applications
- Continuously monitor the use of these resources across the organization
Education will be far more effective than criticism, because after all, shadow IT users have genuine motivations. They just want to get their work done faster and more efficiently.
Step 2: Implement spend management automation
Left unchecked, shadow IT can be a tough process to wind back. Without digital spend management and oversight, it's practically impossible. Armed with the right software program, IT departments and finance teams can dramatically cut instances of shadow IT, by automating expense approvals and reporting.
Step 3: Set category spending limits in IT
Guardrails on IT spending can help too. For example:
- Give your employees the guardrails to buy and use only the very best tools for the job
- Restrict card spending to certain merchants or SaaS companies
- Cap purchase volumes in categories like SaaS, computer hardware, and apps
And don’t worry. Setting category spending limits is not about putting a brake on employee productivity or problem-solving. It’s about ensuring the right resources are used by the right people.
Step 4: Automate IT expense reconciliation
Expense reports take forever and are prone to errors. This is why instant reconciliation is a must-have, especially if it’s able to automatically collect, match, and categorize paper receipts in real-time.
Step 5: Transform IT reimbursement
Paying employees back for business-related expenses has always been a slow and cumbersome process. In fact, it’s one of the main drivers of shadow IT. Often, employees would rather power ahead, buy what they think they need, and ask for forgiveness or permission after the fact.
But now, you can streamline reimbursements by giving employees corporate cards like Ramp that are easy to customize with category limits, spending limits, and merchant limits too.
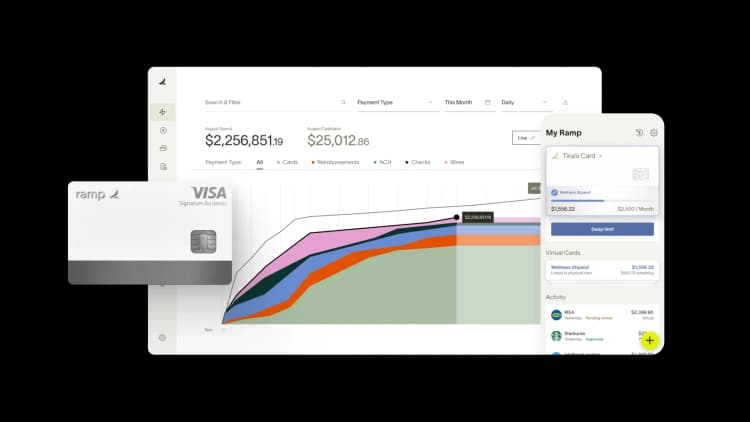
How Ramp helps you regain control over shadow IT spending
Shadow IT spending can quickly spiral out of control when employees purchase software subscriptions without approval, leading to duplicate tools, security risks, and budget overruns. Finance teams often discover these unauthorized purchases only after they've been expensed, making it nearly impossible to manage IT costs effectively or ensure compliance with company policies.
Expense management platforms like Ramp tackle this challenge head-on with proactive spending controls. You can set up custom approval workflows that require authorization before any software purchase goes through, not after. When an employee tries to buy a new SaaS subscription, Ramp automatically routes the request to the appropriate manager or IT administrator based on your predefined rules. This means no more surprise software charges hitting your statements at month-end.
The platform's real-time visibility features give you unprecedented insight into all technology spending across your organization. Ramp automatically categorizes and tracks recurring software subscriptions, making it easy to spot duplicate services or unauthorized tools. You can see exactly who's spending what on which platforms, all from a single dashboard. This transparency helps you identify redundant subscriptions that different departments might be paying for separately, potentially saving thousands in unnecessary costs.
Ramp's virtual cards add another layer of control by letting you issue purpose-specific cards with built-in spending limits and merchant restrictions. You can create cards that only work for approved software vendors or set monthly limits that align with your IT budget. If someone tries to use their card outside these parameters, the transaction gets blocked instantly. This proactive approach transforms shadow IT from an ongoing headache into a manageable, controlled process that protects both your budget and your company's security posture.
Bringing shadow IT into the light
Shadow IT creates zombie spend when employees purchase tools without IT oversight. While you can't eliminate this behavior entirely, you can minimize it through education and trust-building with your team.
The key is verification. Modern spend management makes monitoring expense reports and corporate card usage straightforward—a task that used to require significant manual effort. With the right tools in place, shadow IT becomes far less threatening to your organization's security and budget.
Ready to take control? Get started with Ramp today.

Don't miss these
“We used to pay up to $20k a year for our AP platform. With Ramp, we’re earning back well over that amount. That's money that belongs to the mission now, not to the back-office software.”
Heidi Coffer
Chief Financial Officer, Boys & Girls Clubs of San Francisco

“We're accountable to our funders, our partners, and the families we serve. That accountability starts with how we manage every dollar. Ramp makes it easy for our team to spend wisely, track in real time, and keep overhead low so more resources reach the families navigating infertility.”
Rachel Fruchtman
CFO, Jewish Fertility Foundation

“Each member of our team has an outsized impact due to our focus on using high-leverage tools like Ramp.”
Lauren Feeney
Controller, Perplexity

“With Ramp, we haven’t had to add accounting headcount to keep up with growth. The biggest takeaway is that instead of hiring our way through it, we fixed the workflow so we can keep supporting the organization as we scale.”
Melissa M.
VP of Accounting at Brandt Information Services

“In the public sector, every hour and every dollar belongs to the taxpayer. We can't afford to waste either. Ramp ensures we don't.”
Carly Ching
Finance Specialist, City of Ketchum

“Compared to our previous vendor, Ramp gave us true transaction-level granularity, making it possible for me to audit thousands of transactions in record time.”
Lisa Norris
Director of Compliance & Privacy Officer, ABB Optical

“We chose Ramp because it replaced several disparate tools with one platform our teams actually use—if it’s not in Ramp, it’s not getting paid.”
Michael Bohn
Head of Business Operations, Foursquare

“Ramp gives us one structured intake, one set of guardrails, and clean data end‑to‑end— that’s how we save 20 hours/month and buy back days at close.”
David Eckstein
CFO, Vanta
