Vendor risk management: Definition, risks, and best practices

- What is vendor risk management?
- Why vendor risk management matters
- The vendor risk assessment process
- Building a vendor risk management program
- Best practices for vendor risk management
- Get on top of your vendor management with Ramp
Third-party vendors are essential to how your team runs, but they also widen your attack surface. Vendor risk management (VRM) is how you keep that exposure in check.
Recent incidents, including the 2024 Advance Auto Parts breach tied to a cloud provider, show how a single vendor can expose millions of records and force costly remediation. Meanwhile, the global average cost of a data breach reached $4.88 million in 2024, according to IBM’s Cost of a Data Breach 2024 report.
Vendor risk management means identifying, assessing, and monitoring risks posed by third-party vendors and service providers so you can protect data, meet compliance obligations, and keep operations running.
What is vendor risk management?
Vendor risk management (VRM) protects your company’s security, reputation, and compliance from risks created by third-party relationships. It’s the process of identifying, assessing, and mitigating vendor risks that could affect your operations, from cybersecurity and data privacy to financial and reputational exposure.
Vendor risk management differs from broader vendor management, which focuses on establishing and cultivating relationships with vendors to secure more favorable contract terms, achieve cost savings, and improve performance. Vendor risk management is about protecting your company from any risks associated with your vendors.
You’ll also hear related terms like third-party risk management and supplier risk management. VRM is a subset of third-party risk management, which includes all third-party relationships: vendors, partners, contractors, and service providers. In industries like healthcare, banking, and retail, VRM often centers on protecting sensitive data and meeting HIPAA or PCI obligations.
Vendor risk management in practice
VRM starts before you sign with a vendor and continues for the life of the relationship. Intake captures what the vendor will do, what data it will touch, and which systems it can access. Pre-contract due diligence follows, using questionnaires, certifications, and basic financial checks to size the risk and place the vendor in a tier.
During contracting and onboarding, you bake controls into the agreement—data processing agreements, service level agreements, security obligations, and the right to audit—then scope access tightly with single sign-on (SSO), least-privilege permissions, and data minimization. Approvals and evidence live in one place so they’re easy to audit.
After go-live, you monitor continuously and reassess on a schedule that matches the tier. If an incident occurs, you and the vendor follow a documented playbook with clear owners and timelines. When the relationship ends, offboarding removes access, returns or deletes data, and executes the exit plan.
Key components of vendor risk management
Most VRM programs revolve around four core activities, such as assessment, monitoring, mitigation, and reporting, run on a repeatable cadence.
- Assessment: Evaluate potential risks—e.g., operational capabilities, compliance record, financial health, and technical security—using due-diligence questionnaires and independent audits
- Monitoring: Track performance and any changes in the vendor’s risk profile after onboarding
- Mitigation: Limit access to sensitive data, add security controls, build contingency plans, and consider alternative vendors
- Reporting: Keep stakeholders informed with risk scores, audit trails, and remediation status
All four components run continuously to protect your data and keep decisions auditable.
What is risk scoring in vendor risk management?
Risk scoring is a consistent way to evaluate and compare vendors. Teams assign weights to categories (for example, security, operations, compliance, financial health) and use a simple scale (such as low/moderate/high or 1–5). The score informs tiering, controls, reassessment cadence, and renewal decisions.
Types of vendor risks
Vendor risks typically fall into a few buckets. Use this structure to guide reviews and choose the right controls:
- Operational risks: Service failures or outages that interrupt critical workflows
- Financial risks: Insolvency or contract breaches that create penalties or lost revenue
- Cybersecurity and data privacy risks: Weak controls that raise breach exposure
- Compliance and regulatory risks: Gaps against GDPR, HIPAA, or SOX compliance
- Reputational risks: Incidents that undermine customer trust or brand credibility
| Risk type | Example | Common mitigations |
|---|---|---|
| Operational | SaaS outage halts billing runs | Redundant vendors; SLAs; incident playbooks |
| Financial | Vendor insolvency disrupts services | Financial checks; escrow; exit clauses |
| Cybersecurity and privacy | Third-party breach exposes PII | Least privilege; encryption; SOC 2/ISO review |
| Compliance and regulatory | GDPR/HIPAA gap or audit failure | DPAs; audits; corrective action plans |
| Reputational | Public incident harms brand trust | Communications plan; rapid remediation; vendor audits |
Why vendor risk management matters
Outsourcing critical functions to vendors helps teams move faster and focus on core work. But every integration, data share, and dependency expands your risk surface. Vendor risk management preserves security, compliance, and continuity so one weak link doesn’t become a business-wide incident.
What’s at stake:
- Security and privacy: Vendor access and data flows create new paths for attackers. If controls are weak or outdated, a third party can expose sensitive information.
- Regulatory exposure: Misaligned practices against frameworks and laws, such as SOC 2 controls, ISO/IEC 27001 mappings, or sector rules such as HIPAA,can trigger findings, fines, or remediation orders
- Operational continuity: Outages and performance issues at a key vendor can halt billing runs, slow close processes, delay payroll, or disrupt customer support. Resilience demands service level agreements (SLAs), failover plans, and tested incident playbooks.
- Financial impact: Breaches, downtime, penalties, and emergency migrations are costly. Add in contract penalties, chargebacks, and team time diverted to triage, and the total cost rises quickly.
- Reputational risk: Public incidents erode trust with customers, auditors, and the board. Even after remediation, sales cycles can lengthen and renewals can suffer.
Right-sizing VRM means applying more scrutiny where the stakes are highest—Tier 1 vendors, systems with sensitive data, and services on critical business paths—while keeping friction low for low-risk tools. That balance helps teams stay productive without compromising on protection.
Benefits of effective vendor risk management
When you implement vendor risk management effectively, your business benefits in a few key ways:
- Cost savings and efficiency improvements: Preventing incidents limits remediation, penalties, and lost business while automation reduces manual review and keeps teams focused on higher-value work
- Enhanced security posture: You gain clearer visibility into data flows, access scopes, and control gaps, which makes it easier to apply least privilege, harden systems, and reduce breach exposure
- Better regulatory compliance: Due diligence and contractual controls help you avoid findings and fines while aligning vendors with the standards your industry requires
- Improved business continuity: Visibility and vendor tiering inform contingency plans and failovers so critical operations keep moving even if a provider has an outage
Common vendor risk management challenges
Even with a solid VRM plan, you’ll still run into a few common snags:
- Limited visibility into vendor operations: It’s hard to see behind the scenes—what vendors can access, how they run security, and how their fourth-party subcontractors operate
- Resource constraints: Budgets, time, and expertise are finite, which makes building and maintaining a mature program challenging
- Keeping up with regulatory changes: Rules evolve quickly, so you need vendors to track and meet new standards alongside you
- Managing multiple vendor relationships: As the stack grows, standardizing reviews and controls across different risk profiles gets complex
The vendor risk assessment process
The vendor risk assessment confirms that new and existing vendors meet your security, compliance, and operational standards. It also sets expectations for ongoing monitoring.
To conduct a risk assessment, follow these steps:
- Identification: Define the service the vendor provides and the level of access to your data and operations so you can classify the risk level
- Assessment: Pre-contract, use standardized questionnaires to evaluate legal compliance, financial stability, and technical security, then assign a risk score
- Mitigation: After you identify the risk level, add controls, tighten data access, and include contractual clauses to reduce exposure
- Monitoring: Once approved, continuously track performance, compliance, and any changes that warrant reassessment
Your reassessment cadence depends on the vendor’s risk classification. Always assess before onboarding a new vendor. Post-contract, reassess on a regular schedule and whenever major service changes, regulatory updates, or risk incidents occur.
Pre-contract risk assessment
Evaluate the vendor before you sign. Request security certifications, privacy and data storage policies, evidence of regulatory compliance, and financial statements. Use these documents to score risk across categories such as security, operations, regulatory compliance, and financial health, weighting each category based on relevance to your business. A simple scale (for example, 1–5 or low/moderate/high) makes vendors comparable.
Watch for red flags like:
- Outdated policies
- Lack of security certifications
- Incomplete questionnaires
- History of data breaches
- Vague answers to assessment questions
Ongoing risk monitoring
After vendors have passed the pre-contract assessment and you’ve onboarded them, continue monitoring throughout the relationship. Automated tools can surface security vulnerabilities, legal filings, and financial changes; regular audits keep earlier assumptions current. Track KPIs such as incident response metrics, customer complaints, support issues, and security and privacy compliance. Reassess on a schedule by tier: low risk: as needed or every 1–2 years; moderate risk: annually; high risk: every 6–12 months.
Risk assessment tools and frameworks
Standardized questionnaires and controls frameworks streamline reviews and make them auditable. Common questionnaires include the SIG (Standardized Information Gathering) and CAIQ (Consensus Assessments Initiative Questionnaire), which you should tailor to your industry and data sensitivity. Typical questions cover vulnerability scanning and penetration testing, admin-access controls, incident response, encryption, breach history, and employee security and privacy training.
Industry frameworks to reference include: NIST SP 800-53 or 800-171; ISO/IEC 27001 and 27005; SOC 2 Trust Services Criteria; GDPR frameworks; and HIPAA rules where applicable. Automation can help with continuous monitoring, dashboards, and workflow integrations as your program scales.
Building a vendor risk management program
Creating a formal vendor risk management program is a proactive way to protect your business from third-party threats. Use this step-by-step guide to build yours:
- Define your objectives: First, identify scope and goals for the program. Then, decide who owns the program—whether it’s procurement, compliance, or another internal group.
- Choose a risk framework: Identify the risk types you care about most to focus your framework. Is it data security, financial, operational, or other risks you need to watch?
- Create risk management policies: Develop and document clear policies. Standardize procedures across the vendor lifecycle.
- Develop incident response plans: With your risk types defined, outline proactive playbooks. Define escalation paths and plans for operational disruption.
- Begin risk assessments: With objectives, framework, and policies in place, assess your vendors, mitigate risks, monitor, and report on classifications. Set a review cadence to adjust as risks change.
The success of any vendor risk management program relies on stakeholder buy-in and involvement. Business owners for each vendor, procurement, legal, IT, security, and your executive team should be aligned on your VRM goals, framework, and policy. To gain buy-in, tie VRM to strategic goals, illustrate realistic risk scenarios, and show how strong risk management delivers financial and operational ROI.
Creating vendor risk management policies
As you create vendor risk management policies, include these components:
- Scope: Identify the purpose of your policy and what it covers
- Roles: Define who on your team is responsible for which parts
- Risk assessment criteria: Establish your criteria for evaluating vendors
- Due diligence requirements: Detail the regular checks for ensuring vendors remain compliant
- Monitoring requirements: Explain how you will continuously monitor and assess vendors
- Offboarding procedures: Standardize your process for terminating vendor relationships and removing access to sensitive data
Establish approval processes for new vendors. Set risk-level thresholds so the right stakeholders are involved, and work with procurement and legal to integrate policies into contract workflows before onboarding. After a vendor is onboarded, create a central repository for contracts, risk assessments, vendor compliance documentation, and approval history; time-stamp records with approver names to simplify audits.
What is vendor compliance?
Vendor compliance is a vendor’s adherence to the laws, regulations, frameworks, and contractual obligations that apply to your engagement. It’s verified through certifications and attestations, audits, and periodic reassessments, with remediation plans when gaps appear.
Vendor tiering and categorization
As part of your vendor risk management program, classify vendors by risk level so you can tailor the depth of review and the resources you invest:
Tier 1: High-risk
Vendors with access to your most sensitive data and core systems. Prioritize security and legal resources. Use regular due diligence, annual audits, and frequent reviews of their data security practices.
Tier 2: Moderate-risk
Vendors without access to your most critical systems but with important information access. Automate parts of VRM and set continuous monitoring alerts. Schedule semiannual check-ins and annual questionnaires to ensure ongoing compliance.
Tier 3: Low-risk
Vendors with minimal access to your data, services, or systems. Continue basic due diligence and maintain a light check-in cadence; prioritize higher-risk vendors while keeping continuous monitoring in place for changes.
Vendor compliance requirements
There are three main phases of monitoring vendor compliance: setting standards, monitoring, and handling non-compliance.
- Setting compliance standards: Require vendors to meet your internal security standards, provide regular compliance certifications, and disclose any past breaches
- Monitoring vendor compliance: Conduct periodic reassessments, audit high-risk vendors, and use continuous monitoring
- Handling non-compliance issues: Define escalation paths with remediation timelines and owners, penalties, and potential contract termination
Best practices for vendor risk management
Strong coordination across procurement, legal, IT, security, and finance keeps VRM practical and fast.
- Assign a clear owner: Name a business owner for each vendor and make responsibilities explicit
- Standardize intake: Use a short form that captures data sensitivity, system access, and business criticality up front
- Share the risk picture: Circulate simple vendor scorecards and remediation plans so stakeholders see status at a glance
- Define escalation paths: Document who gets notified, how quickly, and what to do if a vendor fails a control
- Close the loop: Track decisions and approvals in a central system so audits and renewals move faster
Technology and automation
Automation reduces manual effort and keeps signals flowing so you can focus on judgment calls, not busywork.
- Use questionnaires and scoring: Standardize due diligence with a core set of questions and a repeatable scoring model
- Automate monitoring: Pull alerts on security disclosures, financial health changes, and regulatory news for high-risk vendors
- Integrate workflows: Connect intake, assessments, ticketing, and document storage to cut handoffs and rework
- Control access by design: Enforce single sign-on, least privilege, and periodic access reviews for vendor accounts
- Operationalize offboarding: Trigger access removal and data return or deletion steps automatically when a contract ends
Continuous improvement
Treat VRM as an iterative program that gets sharper with each cycle.
- Measure what matters: Track time to assess, time to remediate, reassessment completion by tier, and percentage of vendors with current attestations
- Run exercises and postmortems: Tabletop common failure modes and review real incidents to strengthen playbooks
- Tune tiers and cadence: Revisit risk tiers, reassessment schedules, and control depth as your stack and regulations change
- Update policies and templates: Refresh questionnaires, contract language, and evidence requirements based on findings
- Validate exits: Periodically test vendor offboarding and data deletion so you can prove it works when needed
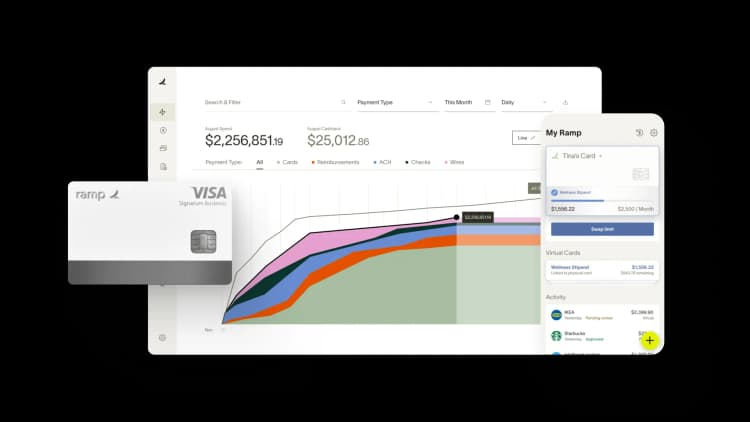
Get on top of your vendor management with Ramp
Vendor risk management helps you manage the security, compliance, and performance of your vendor relationships. By adopting a structured and proactive vendor risk management program, leveraging automation, and utilizing specialized tools, you can protect your business from cybersecurity risks, ensure business continuity, and meet regulatory compliance requirements.
As Forbes reports, effective vendor risk management leads to ROI well beyond the millions you will save from avoiding a data breach. With continuous monitoring, risk scoring, and regular vendor performance reviews, you can mitigate risks and maintain strong, secure vendor partnerships that drive your business forward.
Learn how Ramp’s vendor management platform can help you stay on top of your vendor details as part of your comprehensive risk management program.

FAQs
Vendor management focuses on the relationship—pricing, performance, and service delivery. Vendor risk management (VRM) focuses on protecting your organization from risks introduced by that relationship, such as data exposure, downtime, compliance gaps, and reputational harm.
Every vendor expands your attack surface and operational dependence. VRM reduces the likelihood and impact of issues by requiring due diligence up front, applying risk-based controls, and monitoring vendors over time so problems are caught and addressed early.
Scorecards translate qualitative reviews into comparable measures. By scoring categories like security, privacy, compliance, financial stability, and support, you can prioritize remediation, decide which vendors to onboard or renew, and track improvement over time.
The lifecycle spans intake, pre-contract due diligence, risk-based tiering, contract controls, onboarding checks, continuous monitoring and reassessment, incident response, and offboarding. Treat it as a repeatable process so evidence and decisions are auditable.
Vendor compliance is a vendor’s adherence to the laws, regulations, frameworks, and contractual obligations that apply to your engagement. It’s verified through certifications and attestations, audits, and periodic reassessments, with remediation plans when gaps appear.
Risk scoring is a consistent way to evaluate and compare vendors. Teams assign weights to categories (for example, security, operations, compliance, financial health) and use a simple scale (such as low/moderate/high or 1–5). The score informs tiering, controls, reassessment cadence, and renewal decisions.
“Ramp gives us one structured intake, one set of guardrails, and clean data end‑to‑end— that’s how we save 20 hours/month and buy back days at close.”
David Eckstein
CFO, Vanta

“Ramp is the only vendor that can service all of our employees across the globe in one unified system. They handle multiple currencies seamlessly, integrate with all of our accounting systems, and thanks to their customizable card and policy controls, we're compliant worldwide.” ”
Brandon Zell
Chief Accounting Officer, Notion

“When our teams need something, they usually need it right away. The more time we can save doing all those tedious tasks, the more time we can dedicate to supporting our student-athletes.”
Sarah Harris
Secretary, The University of Tennessee Athletics Foundation, Inc.

“Ramp had everything we were looking for, and even things we weren't looking for. The policy aspects, that's something I never even dreamed of that a purchasing card program could handle.”
Doug Volesky
Director of Finance, City of Mount Vernon

“Switching from Brex to Ramp wasn’t just a platform swap—it was a strategic upgrade that aligned with our mission to be agile, efficient, and financially savvy.”
Lily Liu
CEO, Piñata

“With Ramp, everything lives in one place. You can click into a vendor and see every transaction, invoice, and contract. That didn’t exist in Zip. It’s made approvals much faster because decision-makers aren’t chasing down information—they have it all at their fingertips.”
Ryan Williams
Manager, Contract and Vendor Management, Advisor360°

“The ability to create flexible parameters, such as allowing bookings up to 25% above market rate, has been really good for us. Plus, having all the information within the same platform is really valuable.”
Caroline Hill
Assistant Controller, Sana Benefits

“More vendors are allowing for discounts now, because they’re seeing the quick payment. That started with Ramp—getting everyone paid on time. We’ll get a 1-2% discount for paying early. That doesn’t sound like a lot, but when you’re dealing with hundreds of millions of dollars, it does add up.”
James Hardy
CFO, SAM Construction Group


